Tutorial: Adware, Spyware, What Do I Wear?
Our daily lives have become dependent on programs. Whether we realize it or not, every time we use an electronic device, some program or app is running to enable what we are doing. Some of these programs are ones that we intentionally download to our device to give us access to more content while others are preloaded to work in the background without our knowledge. However, as we become more and more reliant on these programs, it becomes much easier to acquire programs that don't truly benefit us at all. Over the last ten years, many programs have been created that simply exist to get on a device where they can run. Most people have heard of viruses(better described as malware), but many still do not understand the difference between adware, malware, spyware, and junkware. Life online is much easier after understanding where these programs come from, what they do, and how to avoid them.
Featured: Geek Tutorials
What am I looking for?
While there are many types of programs that we want to avoid, all of these programs commonly use the same methods to get access to your computer. The most innocuous of these methods is that of tagging along with another program. If you have ever installed Java, you'll see a checkbox that you must uncheck unless you want to install Ask Toolbar as well. Most people will click through an installation without paying attention to things like this, and so end up with programs they did not intend to install. In this example, both Java and Ask Toolbar are safe programs, but this same method is also used for programs that are much less desirable.
Another common way programs will end up on your computer is a tactic I call bum-wearing-a-suit. It is common for an inferior program to advertise functions that seem to indicate it is worth putting on your computer. Once downloaded and installed to the computer it is common to find that the program is incapable or possibly just inferior at the function it advertised; rarely does the program do what you expected. In many other cases the program that was installed reveals itself to be only a trial, requiring you to spend money before it will function at all.
Finally, many programs will scare you or force you into installing them. If you've ever seen an ad that says “you have exteenbajillion errors,” you probably know that to be false, but many people do not. This is especially common with virus infections because the maker wants their victim to feel like they must install it. It is also common practice with trial programs to show a fake scan result to get you to download and use their real scan. Yet another way this can happen is through ads. Ever try to watch a video on the internet and see the website say “you must install such-and-such codec/media player to watch this video?” What the advertisement is doing is planting the thought “you can get what you want if you give us what we want(installing their program).” In the end, these programs generally don't even allow you to access what you wanted to.
So we know these programs are able to gain access in a variety of ways, but why do they want to? The reason malware attempts to gain access seems to be in order to disrupt your activity or destroy your device, however, this is usually not the case. When dealing with any program of this sort it is best to remember its sole purpose is to make money. Each type of program mentioned at the beginning has a specific way of accomplishing this task.
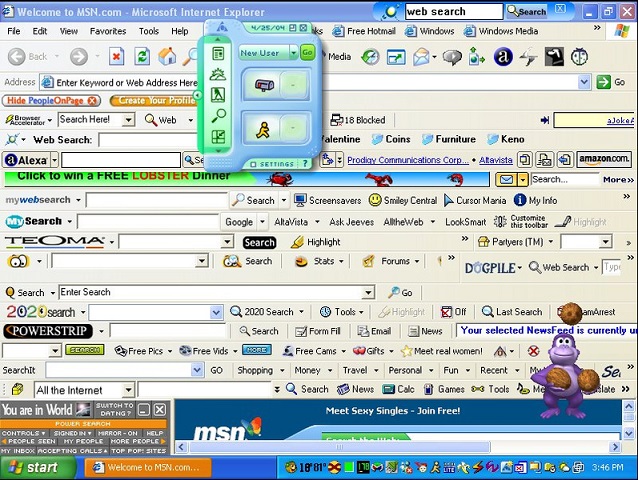
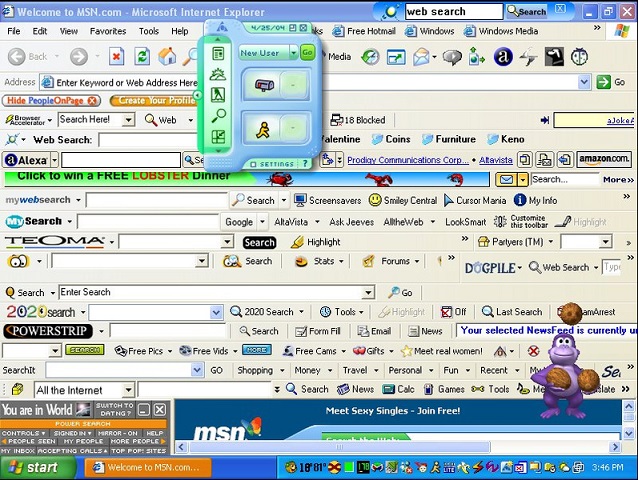
Adware is designed to create ads that pop up at random times on the computer, causing you to click them sometimes even when you meant not to. Each time you click an ad the maker of the program makes about a penny, meaning it needs to be installed on a lot of devices to make any significant money. Malware, known by most as viruses, generally steal personal information or ransom the computer for money. Spyware runs in the background of your computer, tracking what sites you visit and what programs you use. This data is worth money as marketing data once a large sample is collected. Lastly, junkware is software that doesn't do anything. Like the trials mentioned earlier, the program claims to be capable of a function only to reveal that you must pay for something. As a side note to the categories listed above, we could also include toolbars. While most browsing toolbars are not harmful, neither are they needed. Not only do toolbars slow down browsing speed, you can get the search functions of any toolbar by changing your search provider and using the address bar as a search. All of these types of programs should be avoided to keep the computer in optimal condition.

How do I stop spyware?
After reading through the rest of this article you should be starting to get a few ideas of ways you can avoid unwanted programs. Here is a quick reference list in case you missed any.
- Always check for tag-along programs. Any check box present in an installation could be an extra program trying to sneak through.
- Think about what you need. A program may look nifty, but as we said, that's also a trick used to make you want to install it. If you still think you need it, see number three.
- Find and use reputable sources. You need a driver for your incredibly old sound card? Get it from a known driver site, don't install a driver finding program. Need a free .pdf reader? Try cnet.download.com, a well known and reviewed software download site.
- Don't click ads! If you find yourself on a site with many ads, be very careful what and where you are clicking. Sometimes a pop-up will appear and won't seem to close. Always use the red X button to close pop-ups and if the ad pops up a dialog, attempt to X out of that as well. You will also very rarely need to read the text of the dialog box; sometimes the only way out is to click on a specific button that the dialog indicates.
- If a file starts downloading and you didn't start or approve it, shut off your computer(hold the power button till it turns off). While this isn't a very healthy thing to do in a general sense, it is far better than the possibilities of what that foreign file could do.
Programs are everywhere, and they are only going become more and more involved in our lives. By understanding the ways in which programs interact with a computer, we can keep ourselves safe from a hoard of harmful and unwanted programs. It will take some time to get the feel of what is safe and what isn't, but before long you'll be dodging programs like Neo dodged bullets. Just make sure you still use an Anti-Virus program; even Neo could have used one of those.
