The (Literal) Keys To The Internet
“A master key to the internet” might sound at first like a trite plot device from a 2000s B-movie, or like something an out-of-touch congressman might reference at a net neutrality hearing. But the ICANN (Internet Corporation for Associated Names and Numbers) actually does have a key to the Internet. Or rather, it has twenty-one keys.
The non-profit organization issues keys to fourteen primary keyholders and seven backups around the world. These keys unlock safe deposit boxes containing smartcards, which, when activated together at a quarterly meeting, grant access to ICANN’s database of web addresses. Four times each year, the keyholders combine forces to generate a new master key, which allows network infrastructure companies to translate IP addresses into domain names. In particular, the master key produced at the keyholders’ meeting in February was transferred to Verisign, a Virginia infrastructure provider and domain holder which retains the contract for .com domains.
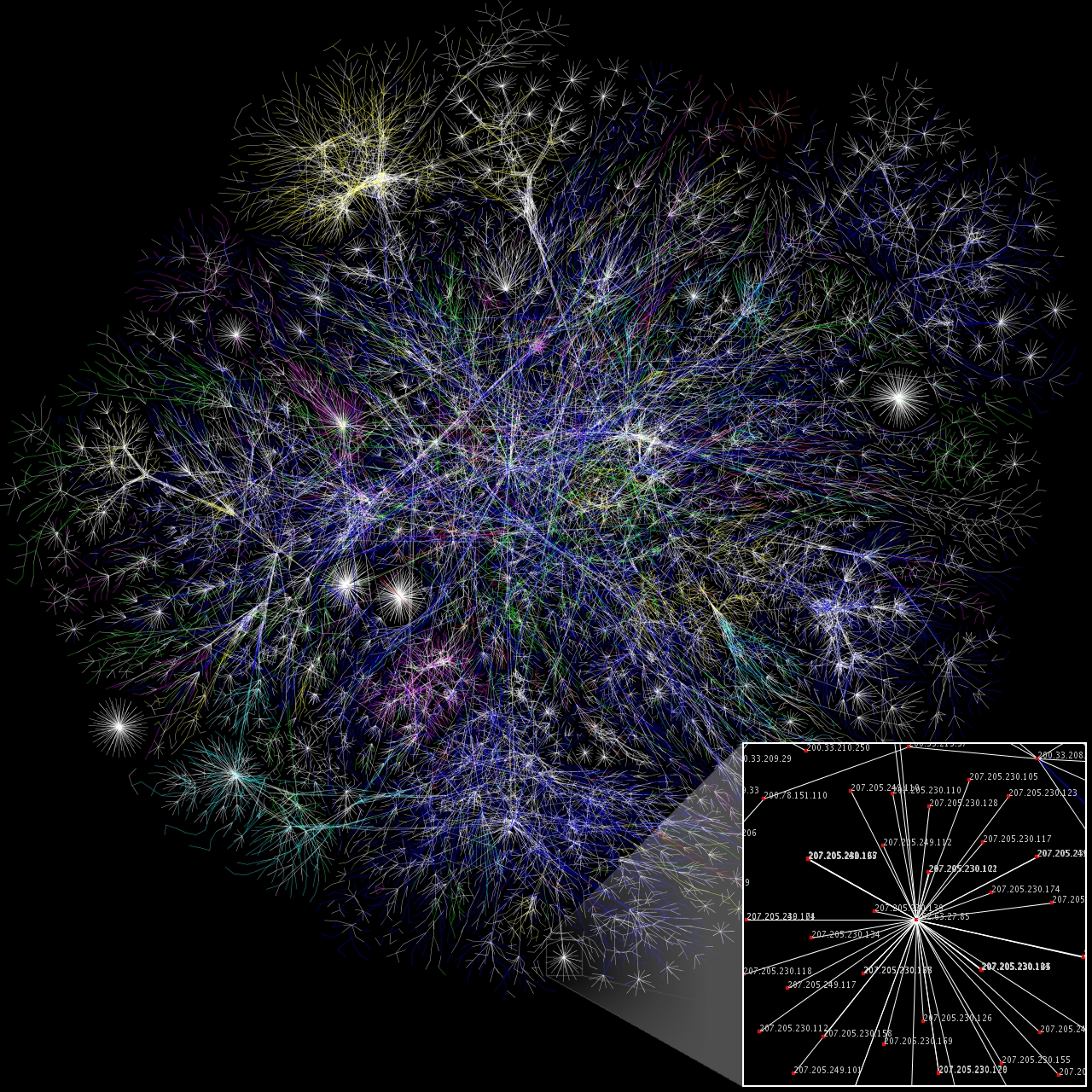
Without the ICANN database, there would be no simple way for network companies like Verisign to link IP address numbers with their corresponding domain names. Instead of entering “geekinsider.com” to get your favorite digital news, you would have to enter “198.90.20.91”. This might not seem like a big deal, but consider the possible consequences of inaccuracies or tampering. If a malicious person or entity were able to change entries in the database, people might be left unable to access basic services they take for granted, like email. If the gmail.com domain name were rerouted to a fake website, users' login information could be easily stolen.
According to The Guardian’s James Ball, the meeting, although sparsely attended and barely publicized, requires intense security measures. This 26-page PDF describes each meticulous step which must be taken to complete the procedure, which takes around five hours total. The steps include many redundant of security measures like USB keys and randomly generated verification strings. This “system based on backups of backups, layers and layers of security” is necessary to generate and maintain trust in the system’s integrity.
To that end, the security features are extremely sensitive. Even the overzealous shutting of a safe is enough to trigger countermeasures calibrated to defend against a seismic event, locking the keyholders into a steel cage. At this ceremony, a few such mishaps occurred, each of which was eventually noted on the official record.
Despite these measures, which might seem excessive, the meetings are not without humor. For example, after the keyholders were locked into a room together until someone could figure out how to bust them out, their first reaction was not to panic but to break out a sleeve of Oreos. As Ball writes, “These steps are a strange mix of high-security measures lifted straight from a thriller (keycards, safe combinations, secure cages), coupled with more mundane technical details – a bit of trouble setting up a printer – and occasional bouts of farce. In short, much like the internet itself.”
Check out James Ball's full article at the Guardian over here.
