Cryptolocker and the Escalating Sophistication of Malicious Internet Attacks
I worked for some time in technical support, remotely accessing computers and resolving issues, or at least attempting to resolve them. Antivirus suites have come a long way in recent years, and there are various excellent free programs available. Furthermore, for the most part, viruses, Trojans and pieces of malware tend to be pretty similar and fairly limited in efficacy, making them quite easy to avoid or eradicate. Cryptolocker, however, deviates from the norm in some nasty and unfortunate ways. What makes it different, and what can be done about it?
Genuine Danger
Infections that serve a financial purpose have traditionally fallen under the umbrella of scareware; this is to say that they generally seek to confuse, intimidate and frighten their victims into paying for the removal of either some invented threats or—more transparently—the infections themselves. They show bombastic messages with big flashing alerts and claims of massive system damage and hope that the users aren’t tech savvy enough to understand what’s happening. While some are more stubborn than others (storing themselves in several locations, perhaps, or sabotaging internet access), they can nevertheless be removed in the same way that their more simplistic brethren can. Boot into Safe Mode, run scans, check AppData—with nothing more than a few pieces of free software, anyone with a basic understanding can get rid of malware.
Cryptolocker is a more formidable opponent. Once it has infected a system, it sets about encrypting the contents of its drives, effectively turning the files into useless gibberish. It then brazenly states that the user will need to pay however much for the key to the decryption process. If the user pays, Cryptolocker puts the files back as they were and removes itself. If they don’t, after a specified period of time the key is deleted and the files are left permanently useless. It’s a rough position to be in because even advanced users are fairly limited in their options. The encryption is absolutely legitimate, and one can easily understand why people would opt to pay the price.
Basic Vigilance
Performing the encryption takes some time; a knowledgeable user could shut off the machine before the process completes. It’s a risky proposition. As such, make sure you have your computer ready just in case.
To start with, back up your files as often as is appropriate given their varying levels of importance. On more than one occasion I’ve seen someone plug in a hard drive and copy the entirety of their Windows partition, but that drains far more time and disk space than is necessary. The Windows files can be replaced easily enough, and anything that exists in the cloud—such as Gmail contacts and emails, or Dropbox contents—can be left alone. Focus on files and documents of personal or professional significance that you don’t have stored anywhere else. That way, if Cryptolocker or something similar rears its ugly head, you can simply reinstall Windows and put everything back.
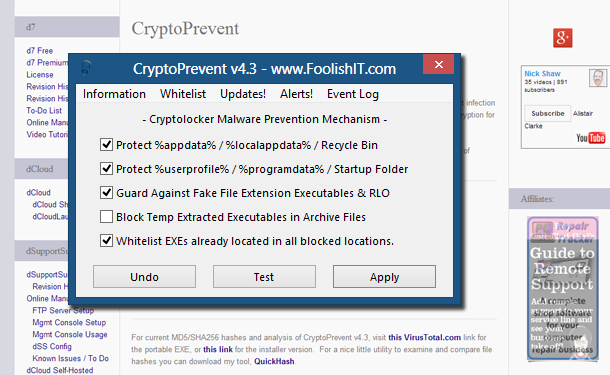
In an ideal world, though, you wouldn’t have to bother reinstalling anything, so you should really just avoid an infection. It can’t get at you if you don’t allow it to run in the first place, so make sure you have antivirus software in place. Microsoft Security Essentials, Avira Antivirus, avast! Free, AVG Free—these are all serviceable free programs that can protect your system well. To be extra safe, you may want to install a small program called Cryptoprevent (screenshot at the top of the page) which does some nifty things like blocking unauthorized executable files in vulnerable locations from running.
Of course, the more you know about how these things work, the safer you’ll be regardless of any software you may use. I know where not to go and what things to avoid, and can get on fine without an enormous suite of protective utilities, so keep in mind that simply exercising sensible judgment will make your computer experience a lot smoother.
Warning Signs
Cryptolocker makes me even happier than I already was that I don’t work in technical support any more. Frankly, it seems like an absolute pain to deal with, and as internet access continues to spread—and online banking goes from strength to strength—the incentive for smart coders to create programs for financial exploitation becomes greater. Still, while the specifics change, the basic remedy is familiar. Plan ahead, back up, be cautious, and if in doubt, do some research; it is so much easier to avoid the dangers if you know how to recognize them.
