Android Apps: Avoiding Certain Permissions
Android Permissions
If you own an android phone, you should take note that your private information is not always handled in a secured manner. For instance, when you purchase an app from the Google Play Store page, it may expose your personal contact information to the developers. There have been instances when the mobile carrier itself started to lift contact information from its users’ phones. In response to all these privacy breaches, stern regulations have been imposed. However, your private information can still be abused by others, if you don’t deal with the apps properly. What makes things worse is many users are completely unaware of these issues.
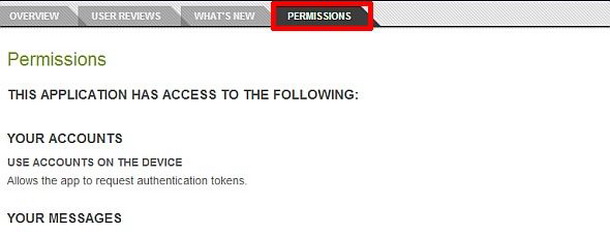
One thing you probably noticed while installing an app is how it asks for certain access to information on your phone. Unfortunately, we generally ignore whatever privacy notifications pop up while installing a new app. We almost all the time, grant whatever access the app is asking for. Even Google can't come up with explanations of what all the different permissions mean – that should tell you a lot right there.
What is Permissions?
These allow android apps to access several features of a phone, such as its hardware details, camera features, photos or other personal details. Some ask for access to your phone’s GPS & data components as well (Google Now asks for this). I agree that many apps from verified sources don’t ask for these permissions with an ill intention. But, Google Play store has malicious apps listed as well!
Through this article, I have tried to list the permissions that you should avoid giving to any Android app. So the next time you install an app, keep a vigilant eye on whether the app is asking for any of these permissions or not.
Reading Log Data
Your handset’s log files can be accessed by the app, if you allow this. For instance, in the case of the CarrierIQ scandal, an app used to secretly email the phone’s log files to the developer. These logs used to contain back logs including keystrokes that made the security violation even worse (It means that even login ids and passwords were included in those back logs).
Processing Outgoing Calls
This permission will allow the app to monitor every minute of detail of outgoing calls. For example, the phone numbers where the calls were made, contact details etc. This permission can be given to the VOIP apps, but if some other app is asking for this, just avoid that permission completely.
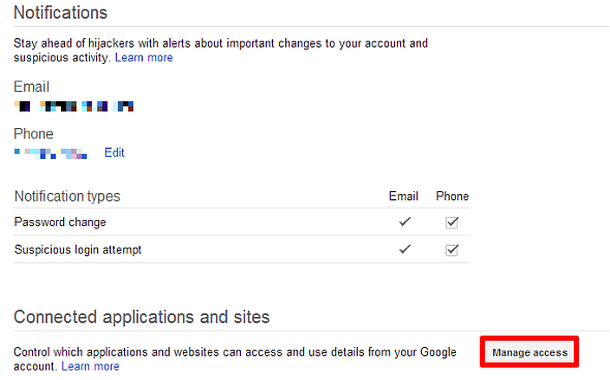
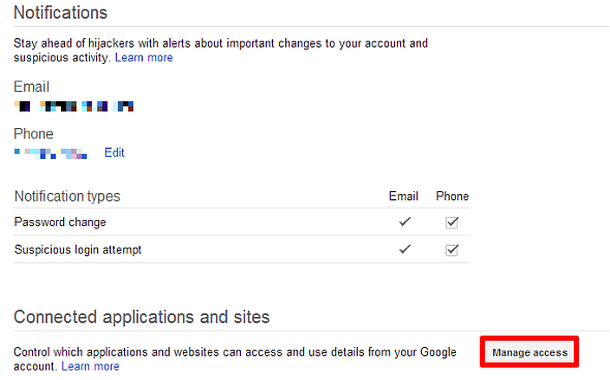
Authenticate Accounts
This lets an app authenticate sensitive information like your account passwords. This is extremely dangerous, making it possible to steal your password details.
I agree that even legitimate apps from developers such as Google, Twitter & Facebook ask for authentication permission (Probably for providing users convenience when they use the respective apps), however, when granting this permission, you have to be very careful.
Write Secure Settings
This is dangerous because it lets the app read or even change the system settings. No legitimate app will ask for this permission. Therefore, if you see an app requesting this, make sure to report it to Google.
Reading Social Stream
This will allow the app to read information from your social feeds. In social networks, we reveal a huge amount of personal information, even this permission can be misused by the wrong app. For example, an average user’s security questions can easily be picked up from the social feed itself.
Read Contacts
Once, I received an email from a friend containing malicious attachments. I was furious and when I called up my friend, he was surprised because he never sent the email. That’s exactly what can happen if a malicious app gets your contact details. They will simply spoof an email and spread their malware through it.
If you need to grant these permissions for whatever reason, please be very careful and make sure its legit.
